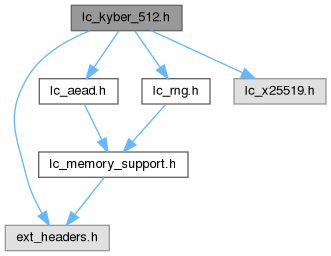
Include dependency graph for lc_kyber_512.h:
Include dependency graph for lc_kyber_512.h:Go to the source code of this file.
Data Structures | |
| struct | lc_kyber_512_sk |
| Kyber secret key. More... | |
| struct | lc_kyber_512_pk |
| Kyber public key. More... | |
| struct | lc_kyber_512_ct |
| Kyber ciphertext. More... | |
| struct | lc_kyber_512_ss |
| Kyber shared secret. More... | |
| struct | lc_kyber_512_x25519_sk |
| Kyber secret key. More... | |
| struct | lc_kyber_512_x25519_pk |
| Kyber public key. More... | |
| struct | lc_kyber_512_x25519_ct |
| Kyber ciphertext. More... | |
| struct | lc_kyber_512_x25519_ss |
| Kyber shared secret. More... | |
Macros | |
| #define | LC_KYBER_X25519_KEM |
Functions | |
| static LC_PURE unsigned int | lc_kyber_512_sk_size (void) |
| Return the size of the Kyber secret key. | |
| static LC_PURE unsigned int | lc_kyber_512_pk_size (void) |
| Return the size of the Kyber public key. | |
| static LC_PURE unsigned int | lc_kyber_512_ct_size (void) |
| Return the size of the Kyber ciphertext. | |
| static LC_PURE unsigned int | lc_kyber_512_ss_size (void) |
| Return the size of the Kyber shared secret. | |
| int | lc_kyber_512_keypair (struct lc_kyber_512_pk *pk, struct lc_kyber_512_sk *sk, struct lc_rng_ctx *rng_ctx) |
| lc_kyber_keypair - Generates public and private key for IND-CCA2-secure Kyber key encapsulation mechanism | |
| int | lc_kyber_512_keypair_from_seed (struct lc_kyber_512_pk *pk, struct lc_kyber_512_sk *sk, const uint8_t *seed, size_t seedlen) |
| lc_kyber__keypair_from_seed - Generates Kyber public and private key from a given seed. | |
| int | lc_kyber_512_enc (struct lc_kyber_512_ct *ct, struct lc_kyber_512_ss *ss, const struct lc_kyber_512_pk *pk) |
| lc_kyber_enc - Key encapsulation | |
| int | lc_kyber_512_enc_kdf (struct lc_kyber_512_ct *ct, uint8_t *ss, size_t ss_len, const struct lc_kyber_512_pk *pk) |
| lc_kyber_512_enc_kdf - Key encapsulation with KDF applied to shared secret | |
| int | lc_kyber_512_dec (struct lc_kyber_512_ss *ss, const struct lc_kyber_512_ct *ct, const struct lc_kyber_512_sk *sk) |
| lc_kyber_dec - Key decapsulation | |
| int | lc_kyber_512_dec_kdf (uint8_t *ss, size_t ss_len, const struct lc_kyber_512_ct *ct, const struct lc_kyber_512_sk *sk) |
| lc_kyber_dec_kdf - Key decapsulation with KDF applied to shared secret | |
| int | lc_kex_512_uake_initiator_init (struct lc_kyber_512_pk *pk_e_i, struct lc_kyber_512_ct *ct_e_i, struct lc_kyber_512_ss *tk, struct lc_kyber_512_sk *sk_e, const struct lc_kyber_512_pk *pk_r) |
| lc_kex_uake_initiator_init - Initialize unilaterally authenticated key exchange | |
| int | lc_kex_512_uake_responder_ss (struct lc_kyber_512_ct *ct_e_r, uint8_t *shared_secret, size_t shared_secret_len, const uint8_t *kdf_nonce, size_t kdf_nonce_len, const struct lc_kyber_512_pk *pk_e_i, const struct lc_kyber_512_ct *ct_e_i, const struct lc_kyber_512_sk *sk_r) |
| lc_kex_uake_responder_ss - Initiator's shared secret generation | |
| int | lc_kex_512_uake_initiator_ss (uint8_t *shared_secret, size_t shared_secret_len, const uint8_t *kdf_nonce, size_t kdf_nonce_len, const struct lc_kyber_512_ct *ct_e_r, const struct lc_kyber_512_ss *tk, const struct lc_kyber_512_sk *sk_e) |
| lc_kex_uake_initiator_ss - Responder's shared secret generation | |
| int | lc_kex_512_ake_initiator_init (struct lc_kyber_512_pk *pk_e_i, struct lc_kyber_512_ct *ct_e_i, struct lc_kyber_512_ss *tk, struct lc_kyber_512_sk *sk_e, const struct lc_kyber_512_pk *pk_r) |
| lc_kex_ake_initiator_init - Initialize authenticated key exchange | |
| int | lc_kex_512_ake_responder_ss (struct lc_kyber_512_ct *ct_e_r_1, struct lc_kyber_512_ct *ct_e_r_2, uint8_t *shared_secret, size_t shared_secret_len, const uint8_t *kdf_nonce, size_t kdf_nonce_len, const struct lc_kyber_512_pk *pk_e_i, const struct lc_kyber_512_ct *ct_e_i, const struct lc_kyber_512_sk *sk_r, const struct lc_kyber_512_pk *pk_i) |
| lc_kex_ake_responder_ss - Initiator's shared secret generation | |
| int | lc_kex_512_ake_initiator_ss (uint8_t *shared_secret, size_t shared_secret_len, const uint8_t *kdf_nonce, size_t kdf_nonce_len, const struct lc_kyber_512_ct *ct_e_r_1, const struct lc_kyber_512_ct *ct_e_r_2, const struct lc_kyber_512_ss *tk, const struct lc_kyber_512_sk *sk_e, const struct lc_kyber_512_sk *sk_i) |
| lc_kex_ake_initiator_ss - Responder's shared secret generation | |
| int | lc_kyber_512_ies_enc (const struct lc_kyber_512_pk *pk, struct lc_kyber_512_ct *ct, const uint8_t *plaintext, uint8_t *ciphertext, size_t datalen, const uint8_t *aad, size_t aadlen, uint8_t *tag, size_t taglen, struct lc_aead_ctx *aead) |
| lc_kyber_ies_enc - KyberIES encryption oneshot | |
| int | lc_kyber_512_ies_enc_init (struct lc_aead_ctx *aead, const struct lc_kyber_512_pk *pk, struct lc_kyber_512_ct *ct, const uint8_t *aad, size_t aadlen) |
| lc_kyber_ies_enc_init - KyberIES encryption stream operation initialization | |
| static int | lc_kyber_512_ies_enc_update (struct lc_aead_ctx *aead, const uint8_t *plaintext, uint8_t *ciphertext, size_t datalen) |
| lc_kyber_ies_enc_update - KyberIES encryption stream operation add more data | |
| static int | lc_kyber_512_ies_enc_final (struct lc_aead_ctx *aead, uint8_t *tag, size_t taglen) |
| lc_kyber_ies_enc_final - KyberIES encryption stream operation finalization / integrity test | |
| int | lc_kyber_512_ies_dec (const struct lc_kyber_512_sk *sk, const struct lc_kyber_512_ct *ct, const uint8_t *ciphertext, uint8_t *plaintext, size_t datalen, const uint8_t *aad, size_t aadlen, const uint8_t *tag, size_t taglen, struct lc_aead_ctx *aead) |
| lc_kyber_ies_dec - KyberIES decryption oneshot | |
| int | lc_kyber_512_ies_dec_init (struct lc_aead_ctx *aead, const struct lc_kyber_512_sk *sk, const struct lc_kyber_512_ct *ct, const uint8_t *aad, size_t aadlen) |
| lc_kyber_ies_dec_init - KyberIES decryption stream operation initialization | |
| static int | lc_kyber_512_ies_dec_update (struct lc_aead_ctx *aead, const uint8_t *ciphertext, uint8_t *plaintext, size_t datalen) |
| lc_kyber_ies_dec_update - KyberIES decryption stream operation add more data | |
| static int | lc_kyber_512_ies_dec_final (struct lc_aead_ctx *aead, const uint8_t *tag, size_t taglen) |
| lc_kyber_ies_dec_final - KyberIES decryption stream operation finalization / integrity test | |
| int | lc_kyber_512_x25519_keypair (struct lc_kyber_512_x25519_pk *pk, struct lc_kyber_512_x25519_sk *sk, struct lc_rng_ctx *rng_ctx) |
| lc_kyber_x25519_keypair - Generates public and private key for IND-CCA2-secure Kyber key encapsulation mechanism | |
| int | lc_kyber_512_x25519_enc_kdf (struct lc_kyber_512_x25519_ct *ct, uint8_t *ss, size_t ss_len, const struct lc_kyber_512_x25519_pk *pk) |
| lc_kyber_x25519_enc_kdf - Key encapsulation with KDF applied to shared secret | |
| int | lc_kyber_512_x25519_dec_kdf (uint8_t *ss, size_t ss_len, const struct lc_kyber_512_x25519_ct *ct, const struct lc_kyber_512_x25519_sk *sk) |
| lc_kyber_x25519_dec_kdf - Key decapsulation with KDF applied to shared secret | |
| int | lc_kex_512_x25519_uake_initiator_init (struct lc_kyber_512_x25519_pk *pk_e_i, struct lc_kyber_512_x25519_ct *ct_e_i, struct lc_kyber_512_x25519_ss *tk, struct lc_kyber_512_x25519_sk *sk_e, const struct lc_kyber_512_x25519_pk *pk_r) |
| lc_kex_x25519_uake_initiator_init - Initialize unilaterally authenticated key exchange | |
| int | lc_kex_512_x25519_uake_responder_ss (struct lc_kyber_512_x25519_ct *ct_e_r, uint8_t *shared_secret, size_t shared_secret_len, const uint8_t *kdf_nonce, size_t kdf_nonce_len, const struct lc_kyber_512_x25519_pk *pk_e_i, const struct lc_kyber_512_x25519_ct *ct_e_i, const struct lc_kyber_512_x25519_sk *sk_r) |
| lc_kex_x25519_uake_responder_ss - Initiator's shared secret generation | |
| int | lc_kex_512_x25519_uake_initiator_ss (uint8_t *shared_secret, size_t shared_secret_len, const uint8_t *kdf_nonce, size_t kdf_nonce_len, const struct lc_kyber_512_x25519_ct *ct_e_r, const struct lc_kyber_512_x25519_ss *tk, const struct lc_kyber_512_x25519_sk *sk_e) |
| lc_kex_x25519_uake_initiator_ss - Responder's shared secret generation | |
| int | lc_kex_512_x25519_ake_initiator_init (struct lc_kyber_512_x25519_pk *pk_e_i, struct lc_kyber_512_x25519_ct *ct_e_i, struct lc_kyber_512_x25519_ss *tk, struct lc_kyber_512_x25519_sk *sk_e, const struct lc_kyber_512_x25519_pk *pk_r) |
| lc_kex_x25519_ake_initiator_init - Initialize authenticated key exchange | |
| int | lc_kex_512_x25519_ake_responder_ss (struct lc_kyber_512_x25519_ct *ct_e_r_1, struct lc_kyber_512_x25519_ct *ct_e_r_2, uint8_t *shared_secret, size_t shared_secret_len, const uint8_t *kdf_nonce, size_t kdf_nonce_len, const struct lc_kyber_512_x25519_pk *pk_e_i, const struct lc_kyber_512_x25519_ct *ct_e_i, const struct lc_kyber_512_x25519_sk *sk_r, const struct lc_kyber_512_x25519_pk *pk_i) |
| lc_kex_x25519_ake_responder_ss - Initiator's shared secret generation | |
| int | lc_kex_512_x25519_ake_initiator_ss (uint8_t *shared_secret, size_t shared_secret_len, const uint8_t *kdf_nonce, size_t kdf_nonce_len, const struct lc_kyber_512_x25519_ct *ct_e_r_1, const struct lc_kyber_512_x25519_ct *ct_e_r_2, const struct lc_kyber_512_x25519_ss *tk, const struct lc_kyber_512_x25519_sk *sk_e, const struct lc_kyber_512_x25519_sk *sk_i) |
| lc_kex_x25519_ake_initiator_ss - Responder's shared secret generation | |
| int | lc_kyber_512_x25519_ies_enc (const struct lc_kyber_512_x25519_pk *pk, struct lc_kyber_512_x25519_ct *ct, const uint8_t *plaintext, uint8_t *ciphertext, size_t datalen, const uint8_t *aad, size_t aadlen, uint8_t *tag, size_t taglen, struct lc_aead_ctx *aead) |
| lc_kyber_x25519_ies_enc - KyberIES encryption oneshot | |
| int | lc_kyber_512_x25519_ies_enc_init (struct lc_aead_ctx *aead, const struct lc_kyber_512_x25519_pk *pk, struct lc_kyber_512_x25519_ct *ct, const uint8_t *aad, size_t aadlen) |
| lc_kyber_x25519_ies_enc_init - KyberIES encryption stream operation initialization | |
| static int | lc_kyber_512_x25519_ies_enc_update (struct lc_aead_ctx *aead, const uint8_t *plaintext, uint8_t *ciphertext, size_t datalen) |
| lc_kyber_x25519_ies_enc_update - KyberIES encryption stream operation add more data | |
| static int | lc_kyber_512_x25519_ies_enc_final (struct lc_aead_ctx *aead, uint8_t *tag, size_t taglen) |
| lc_kyber_x25519_ies_enc_final - KyberIES encryption stream operation finalization / integrity test | |
| int | lc_kyber_512_x25519_ies_dec (const struct lc_kyber_512_x25519_sk *sk, const struct lc_kyber_512_x25519_ct *ct, const uint8_t *ciphertext, uint8_t *plaintext, size_t datalen, const uint8_t *aad, size_t aadlen, const uint8_t *tag, size_t taglen, struct lc_aead_ctx *aead) |
| lc_kyber_x25519_ies_dec - KyberIES decryption oneshot | |
| int | lc_kyber_512_x25519_ies_dec_init (struct lc_aead_ctx *aead, const struct lc_kyber_512_x25519_sk *sk, const struct lc_kyber_512_x25519_ct *ct, const uint8_t *aad, size_t aadlen) |
| lc_kyber_x25519_ies_dec_init - KyberIES decryption stream operation initialization | |
| static int | lc_kyber_512_x25519_ies_dec_update (struct lc_aead_ctx *aead, const uint8_t *ciphertext, uint8_t *plaintext, size_t datalen) |
| lc_kyber_x25519_ies_dec_update - KyberIES decryption stream operation add more data | |
| static int | lc_kyber_512_x25519_ies_dec_final (struct lc_aead_ctx *aead, const uint8_t *tag, size_t taglen) |
| lc_kyber _x25519_ies_dec_final - KyberIES decryption stream operation finalization / integrity test | |
Data Structure Documentation
◆ lc_kyber_512_sk
| struct lc_kyber_512_sk |
Kyber secret key.
General KEM API considerations:
- all APIs starting with lc_kyber_512 / lc_kex_512 use Kyber-512
- all APIs starting with lc_kyber_768 / lc_kex_768 use Kyber-768
- all APIs starting with lc_kyber_1024 / lc_kex_1024 use Kyber-1024
Definition at line 116 of file lc_kyber_512.h.
| Data Fields | ||
|---|---|---|
| uint8_t | sk[LC_KYBER_SECRETKEYBYTES] | |
◆ lc_kyber_512_pk
| struct lc_kyber_512_pk |
Kyber public key.
Definition at line 123 of file lc_kyber_512.h.
| Data Fields | ||
|---|---|---|
| uint8_t | pk[LC_KYBER_PUBLICKEYBYTES] | |
◆ lc_kyber_512_ct
| struct lc_kyber_512_ct |
Kyber ciphertext.
Definition at line 130 of file lc_kyber_512.h.
| Data Fields | ||
|---|---|---|
| uint8_t | ct[LC_CRYPTO_CIPHERTEXTBYTES] | |
◆ lc_kyber_512_ss
| struct lc_kyber_512_ss |
Kyber shared secret.
Definition at line 137 of file lc_kyber_512.h.
| Data Fields | ||
|---|---|---|
| uint8_t | ss[LC_KYBER_SSBYTES] | |
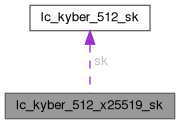
◆ lc_kyber_512_x25519_sk
| struct lc_kyber_512_x25519_sk |
Kyber secret key.
Definition at line 782 of file lc_kyber_512.h.
 Collaboration diagram for lc_kyber_512_x25519_sk:
Collaboration diagram for lc_kyber_512_x25519_sk:| Data Fields | ||
|---|---|---|
| struct lc_kyber_512_sk | sk | |
| struct lc_x25519_sk | sk_x25519 | |
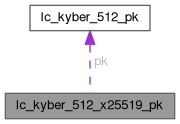
◆ lc_kyber_512_x25519_pk
| struct lc_kyber_512_x25519_pk |
Kyber public key.
Definition at line 790 of file lc_kyber_512.h.
 Collaboration diagram for lc_kyber_512_x25519_pk:
Collaboration diagram for lc_kyber_512_x25519_pk:| Data Fields | ||
|---|---|---|
| struct lc_kyber_512_pk | pk | |
| struct lc_x25519_pk | pk_x25519 | |
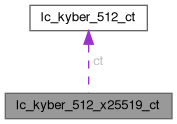
◆ lc_kyber_512_x25519_ct
| struct lc_kyber_512_x25519_ct |
Kyber ciphertext.
Definition at line 798 of file lc_kyber_512.h.
 Collaboration diagram for lc_kyber_512_x25519_ct:
Collaboration diagram for lc_kyber_512_x25519_ct:| Data Fields | ||
|---|---|---|
| struct lc_kyber_512_ct | ct | |
| struct lc_x25519_pk | pk_x25519 | |
◆ lc_kyber_512_x25519_ss
| struct lc_kyber_512_x25519_ss |
Kyber shared secret.
Definition at line 806 of file lc_kyber_512.h.
 Collaboration diagram for lc_kyber_512_x25519_ss:
Collaboration diagram for lc_kyber_512_x25519_ss:| Data Fields | ||
|---|---|---|
| struct lc_kyber_512_ss | ss | |
| struct lc_x25519_ss | ss_x25519 | |
Macro Definition Documentation
◆ LC_KYBER_X25519_KEM
| #define LC_KYBER_X25519_KEM |
Definition at line 774 of file lc_kyber_512.h.
Function Documentation
◆ lc_kex_512_ake_initiator_init()
| int lc_kex_512_ake_initiator_init | ( | struct lc_kyber_512_pk * | pk_e_i, |
| struct lc_kyber_512_ct * | ct_e_i, | ||
| struct lc_kyber_512_ss * | tk, | ||
| struct lc_kyber_512_sk * | sk_e, | ||
| const struct lc_kyber_512_pk * | pk_r ) |
lc_kex_ake_initiator_init - Initialize authenticated key exchange
Authenticated key exchange
The key exchange provides a shared secret between two communication parties. The initiator and responder authenticates the key exchange with their private keys.
The idea is that the pk_i/sk_i and pk_r/sk_r key pairs are static key pairs that are generated and exchanged before the KEX handshake. For the authenticated key exchange, both sides use the respective peer's public key which implies either side authenticates the other end.
- Parameters
-
[out] pk_e_i initiator's ephemeral public key to be sent to the responder [out] ct_e_i initiator's ephemeral cipher text to be sent to the responder [out] tk KEM shared secret data to be used for the initiator's shared secret generation [out] sk_e initiator's ephemeral secret key to be used for the initiator's shared secret generation [in] pk_r responder's public key
- Returns
- 0 (success) or < 0 on error
◆ lc_kex_512_ake_initiator_ss()
| int lc_kex_512_ake_initiator_ss | ( | uint8_t * | shared_secret, |
| size_t | shared_secret_len, | ||
| const uint8_t * | kdf_nonce, | ||
| size_t | kdf_nonce_len, | ||
| const struct lc_kyber_512_ct * | ct_e_r_1, | ||
| const struct lc_kyber_512_ct * | ct_e_r_2, | ||
| const struct lc_kyber_512_ss * | tk, | ||
| const struct lc_kyber_512_sk * | sk_e, | ||
| const struct lc_kyber_512_sk * | sk_i ) |
lc_kex_ake_initiator_ss - Responder's shared secret generation
- Parameters
-
[out] shared_secret Shared secret between initiator and responder [in] shared_secret_len Requested size of the shared secret [in] kdf_nonce An optional nonce that is concatenated at the end of the Kyber KEX-generated data to be inserted into the KDF. If not required, use NULL. [in] kdf_nonce_len Length of the kdf_nonce. [in] ct_e_r_1 responder's ephemeral cipher text [in] ct_e_r_2 responder's ephemeral cipher text [in] tk KEM shared secret data that was generated during the initator's initialization [in] sk_e initator's ephemeral secret that was generated during the initator's initialization [in] sk_i initator's secret key
- Returns
- 0 (success) or < 0 on error
◆ lc_kex_512_ake_responder_ss()
| int lc_kex_512_ake_responder_ss | ( | struct lc_kyber_512_ct * | ct_e_r_1, |
| struct lc_kyber_512_ct * | ct_e_r_2, | ||
| uint8_t * | shared_secret, | ||
| size_t | shared_secret_len, | ||
| const uint8_t * | kdf_nonce, | ||
| size_t | kdf_nonce_len, | ||
| const struct lc_kyber_512_pk * | pk_e_i, | ||
| const struct lc_kyber_512_ct * | ct_e_i, | ||
| const struct lc_kyber_512_sk * | sk_r, | ||
| const struct lc_kyber_512_pk * | pk_i ) |
lc_kex_ake_responder_ss - Initiator's shared secret generation
- Parameters
-
[out] ct_e_r_1 responder's ephemeral cipher text to be sent to the initator [out] ct_e_r_2 responder's ephemeral cipher text to be sent to the initator [out] shared_secret Shared secret between initiator and responder [in] shared_secret_len Requested size of the shared secret [in] kdf_nonce An optional nonce that is concatenated at the end of the Kyber KEX-generated data to be inserted into the KDF. If not required, use NULL. [in] kdf_nonce_len Length of the kdf_nonce. [in] pk_e_i initator's ephemeral public key [in] ct_e_i initator's ephemeral cipher text [in] sk_r responder's secret key [in] pk_i initator's public key
- Returns
- 0 (success) or < 0 on error
◆ lc_kex_512_uake_initiator_init()
| int lc_kex_512_uake_initiator_init | ( | struct lc_kyber_512_pk * | pk_e_i, |
| struct lc_kyber_512_ct * | ct_e_i, | ||
| struct lc_kyber_512_ss * | tk, | ||
| struct lc_kyber_512_sk * | sk_e, | ||
| const struct lc_kyber_512_pk * | pk_r ) |
lc_kex_uake_initiator_init - Initialize unilaterally authenticated key exchange
Unilaterally authenticated key exchange
The key exchange provides a shared secret between two communication parties. Only the initiator authenticates the key exchange with his private key.
The idea is that the pk_r/sk_r key pair is a static key pair that is generated and exchanged before the KEX handshake. For the unilaterally authenticated key exchange, only the initiator uses the responder's public key which implies that the initiator authenticates the responder.
- Parameters
-
[out] pk_e_i initiator's ephemeral public key to be sent to the responder [out] ct_e_i initiator's ephemeral cipher text to be sent to the responder [out] tk KEM shared secret data to be used for the initiator's shared secret generation [out] sk_e initiator's ephemeral secret key to be used for the initiator's shared secret generation [in] pk_r responder's public key
- Returns
- 0 (success) or < 0 on error
◆ lc_kex_512_uake_initiator_ss()
| int lc_kex_512_uake_initiator_ss | ( | uint8_t * | shared_secret, |
| size_t | shared_secret_len, | ||
| const uint8_t * | kdf_nonce, | ||
| size_t | kdf_nonce_len, | ||
| const struct lc_kyber_512_ct * | ct_e_r, | ||
| const struct lc_kyber_512_ss * | tk, | ||
| const struct lc_kyber_512_sk * | sk_e ) |
lc_kex_uake_initiator_ss - Responder's shared secret generation
- Parameters
-
[out] shared_secret Shared secret between initiator and responder [in] shared_secret_len Requested size of the shared secret [in] kdf_nonce An optional nonce that is concatenated at the end of the Kyber KEX-generated data to be inserted into the KDF. If not required, use NULL. [in] kdf_nonce_len Length of the kdf_nonce. [in] ct_e_r responder's ephemeral cipher text [in] tk KEM shared secret data that was generated during the initiator's initialization [in] sk_e initiator's ephemeral secret that was generated during the initiator's initialization
- Returns
- 0 (success) or < 0 on error
◆ lc_kex_512_uake_responder_ss()
| int lc_kex_512_uake_responder_ss | ( | struct lc_kyber_512_ct * | ct_e_r, |
| uint8_t * | shared_secret, | ||
| size_t | shared_secret_len, | ||
| const uint8_t * | kdf_nonce, | ||
| size_t | kdf_nonce_len, | ||
| const struct lc_kyber_512_pk * | pk_e_i, | ||
| const struct lc_kyber_512_ct * | ct_e_i, | ||
| const struct lc_kyber_512_sk * | sk_r ) |
lc_kex_uake_responder_ss - Initiator's shared secret generation
- Parameters
-
[out] ct_e_r responder's ephemeral cipher text to be sent to the initiator [out] shared_secret Shared secret between initiator and responder [in] shared_secret_len Requested size of the shared secret [in] kdf_nonce An optional nonce that is concatenated at the end of the Kyber KEX-generated data to be inserted into the KDF. If not required, use NULL. [in] kdf_nonce_len Length of the kdf_nonce. [in] pk_e_i initiator's ephemeral public key [in] ct_e_i initiator's ephemeral cipher text [in] sk_r responder's secret key
- Returns
- 0 (success) or < 0 on error
◆ lc_kex_512_x25519_ake_initiator_init()
| int lc_kex_512_x25519_ake_initiator_init | ( | struct lc_kyber_512_x25519_pk * | pk_e_i, |
| struct lc_kyber_512_x25519_ct * | ct_e_i, | ||
| struct lc_kyber_512_x25519_ss * | tk, | ||
| struct lc_kyber_512_x25519_sk * | sk_e, | ||
| const struct lc_kyber_512_x25519_pk * | pk_r ) |
lc_kex_x25519_ake_initiator_init - Initialize authenticated key exchange
- Parameters
-
[out] pk_e_i initiator's ephemeral public key to be sent to the responder [out] ct_e_i initiator's ephemeral cipher text to be sent to the responder [out] tk KEM shared secret data to be used for the initiator's shared secret generation [out] sk_e initiator's ephemeral secret key to be used for the initiator's shared secret generation [in] pk_r responder's public key
- Returns
- 0 (success) or < 0 on error
◆ lc_kex_512_x25519_ake_initiator_ss()
| int lc_kex_512_x25519_ake_initiator_ss | ( | uint8_t * | shared_secret, |
| size_t | shared_secret_len, | ||
| const uint8_t * | kdf_nonce, | ||
| size_t | kdf_nonce_len, | ||
| const struct lc_kyber_512_x25519_ct * | ct_e_r_1, | ||
| const struct lc_kyber_512_x25519_ct * | ct_e_r_2, | ||
| const struct lc_kyber_512_x25519_ss * | tk, | ||
| const struct lc_kyber_512_x25519_sk * | sk_e, | ||
| const struct lc_kyber_512_x25519_sk * | sk_i ) |
lc_kex_x25519_ake_initiator_ss - Responder's shared secret generation
- Parameters
-
[out] shared_secret Shared secret between initiator and responder [in] shared_secret_len Requested size of the shared secret [in] kdf_nonce An optional nonce that is concatenated at the end of the Kyber KEX-generated data to be inserted into the KDF. If not required, use NULL. [in] kdf_nonce_len Length of the kdf_nonce. [in] ct_e_r_1 responder's ephemeral cipher text [in] ct_e_r_2 responder's ephemeral cipher text [in] tk KEM shared secret data that was generated during the initator's initialization [in] sk_e initator's ephemeral secret that was generated during the initator's initialization [in] sk_i initator's secret key
- Returns
- 0 (success) or < 0 on error
◆ lc_kex_512_x25519_ake_responder_ss()
| int lc_kex_512_x25519_ake_responder_ss | ( | struct lc_kyber_512_x25519_ct * | ct_e_r_1, |
| struct lc_kyber_512_x25519_ct * | ct_e_r_2, | ||
| uint8_t * | shared_secret, | ||
| size_t | shared_secret_len, | ||
| const uint8_t * | kdf_nonce, | ||
| size_t | kdf_nonce_len, | ||
| const struct lc_kyber_512_x25519_pk * | pk_e_i, | ||
| const struct lc_kyber_512_x25519_ct * | ct_e_i, | ||
| const struct lc_kyber_512_x25519_sk * | sk_r, | ||
| const struct lc_kyber_512_x25519_pk * | pk_i ) |
lc_kex_x25519_ake_responder_ss - Initiator's shared secret generation
- Parameters
-
[out] ct_e_r_1 responder's ephemeral cipher text to be sent to the initator [out] ct_e_r_2 responder's ephemeral cipher text to be sent to the initator [out] shared_secret Shared secret between initiator and responder [in] shared_secret_len Requested size of the shared secret [in] kdf_nonce An optional nonce that is concatenated at the end of the Kyber KEX-generated data to be inserted into the KDF. If not required, use NULL. [in] kdf_nonce_len Length of the kdf_nonce. [in] pk_e_i initator's ephemeral public key [in] ct_e_i initator's ephemeral cipher text [in] sk_r responder's secret key [in] pk_i initator's public key
- Returns
- 0 (success) or < 0 on error
◆ lc_kex_512_x25519_uake_initiator_init()
| int lc_kex_512_x25519_uake_initiator_init | ( | struct lc_kyber_512_x25519_pk * | pk_e_i, |
| struct lc_kyber_512_x25519_ct * | ct_e_i, | ||
| struct lc_kyber_512_x25519_ss * | tk, | ||
| struct lc_kyber_512_x25519_sk * | sk_e, | ||
| const struct lc_kyber_512_x25519_pk * | pk_r ) |
lc_kex_x25519_uake_initiator_init - Initialize unilaterally authenticated key exchange
- Parameters
-
[out] pk_e_i initiator's ephemeral public key to be sent to the responder [out] ct_e_i initiator's ephemeral cipher text to be sent to the responder [out] tk KEM shared secret data to be used for the initiator's shared secret generation [out] sk_e initiator's ephemeral secret key to be used for the initiator's shared secret generation [in] pk_r responder's public key
- Returns
- 0 (success) or < 0 on error
◆ lc_kex_512_x25519_uake_initiator_ss()
| int lc_kex_512_x25519_uake_initiator_ss | ( | uint8_t * | shared_secret, |
| size_t | shared_secret_len, | ||
| const uint8_t * | kdf_nonce, | ||
| size_t | kdf_nonce_len, | ||
| const struct lc_kyber_512_x25519_ct * | ct_e_r, | ||
| const struct lc_kyber_512_x25519_ss * | tk, | ||
| const struct lc_kyber_512_x25519_sk * | sk_e ) |
lc_kex_x25519_uake_initiator_ss - Responder's shared secret generation
- Parameters
-
[out] shared_secret Shared secret between initiator and responder [in] shared_secret_len Requested size of the shared secret [in] kdf_nonce An optional nonce that is concatenated at the end of the Kyber KEX-generated data to be inserted into the KDF. If not required, use NULL. [in] kdf_nonce_len Length of the kdf_nonce. [in] ct_e_r responder's ephemeral cipher text [in] tk KEM shared secret data that was generated during the initiator's initialization [in] sk_e initiator's ephemeral secret that was generated during the initiator's initialization
- Returns
- 0 (success) or < 0 on error
◆ lc_kex_512_x25519_uake_responder_ss()
| int lc_kex_512_x25519_uake_responder_ss | ( | struct lc_kyber_512_x25519_ct * | ct_e_r, |
| uint8_t * | shared_secret, | ||
| size_t | shared_secret_len, | ||
| const uint8_t * | kdf_nonce, | ||
| size_t | kdf_nonce_len, | ||
| const struct lc_kyber_512_x25519_pk * | pk_e_i, | ||
| const struct lc_kyber_512_x25519_ct * | ct_e_i, | ||
| const struct lc_kyber_512_x25519_sk * | sk_r ) |
lc_kex_x25519_uake_responder_ss - Initiator's shared secret generation
- Parameters
-
[out] ct_e_r responder's ephemeral cipher text to be sent to the initiator [out] shared_secret Shared secret between initiator and responder [in] shared_secret_len Requested size of the shared secret [in] kdf_nonce An optional nonce that is concatenated at the end of the Kyber KEX-generated data to be inserted into the KDF. If not required, use NULL. [in] kdf_nonce_len Length of the kdf_nonce. [in] pk_e_i initiator's ephemeral public key [in] ct_e_i initiator's ephemeral cipher text [in] sk_r responder's secret key
- Returns
- 0 (success) or < 0 on error
◆ lc_kyber_512_ct_size()
|
inlinestatic |
Return the size of the Kyber ciphertext.
Definition at line 163 of file lc_kyber_512.h.
◆ lc_kyber_512_dec()
| int lc_kyber_512_dec | ( | struct lc_kyber_512_ss * | ss, |
| const struct lc_kyber_512_ct * | ct, | ||
| const struct lc_kyber_512_sk * | sk ) |
lc_kyber_dec - Key decapsulation
Generates shared secret for given cipher text and private key
- Parameters
-
[out] ss pointer to output shared secret that is the same as produced during encapsulation [in] ct pointer to input cipher text generated during encapsulation [in] sk pointer to input private key
- Returns
- 0
On failure, ss will contain a pseudo-random value.
◆ lc_kyber_512_dec_kdf()
| int lc_kyber_512_dec_kdf | ( | uint8_t * | ss, |
| size_t | ss_len, | ||
| const struct lc_kyber_512_ct * | ct, | ||
| const struct lc_kyber_512_sk * | sk ) |
lc_kyber_dec_kdf - Key decapsulation with KDF applied to shared secret
Generates cipher text and shared secret for given private key. The shared secret is derived from the Kyber SS using the KDF derived from the round 3 definition of Kyber:
SS <- KMAC256(K = Kyber-SS, X = Kyber-CT, L = requested SS length,
S = "Kyber KEM SS")
- Parameters
-
[out] ss pointer to output shared secret that is the same as produced during encapsulation [in] ss_len length of shared secret to be generated [in] ct pointer to input cipher text generated during encapsulation [in] sk pointer to input private key
- Returns
- 0
On failure, ss will contain a pseudo-random value.
◆ lc_kyber_512_enc()
| int lc_kyber_512_enc | ( | struct lc_kyber_512_ct * | ct, |
| struct lc_kyber_512_ss * | ss, | ||
| const struct lc_kyber_512_pk * | pk ) |
lc_kyber_enc - Key encapsulation
Generates cipher text and shared secret for given public key.
- Parameters
-
[out] ct pointer to output cipher text to used for decapsulation [out] ss pointer to output shared secret that will be also produced during decapsulation [in] pk pointer to input public key
Returns 0 (success) or < 0 on error
◆ lc_kyber_512_enc_kdf()
| int lc_kyber_512_enc_kdf | ( | struct lc_kyber_512_ct * | ct, |
| uint8_t * | ss, | ||
| size_t | ss_len, | ||
| const struct lc_kyber_512_pk * | pk ) |
lc_kyber_512_enc_kdf - Key encapsulation with KDF applied to shared secret
Generates cipher text and shared secret for given public key. The shared secret is derived from the Kyber SS using the KDF derived from the round 3 definition of Kyber:
SS <- KMAC256(K = Kyber-SS, X = Kyber-CT, L = requested SS length,
S = "Kyber KEM SS")
- Parameters
-
[out] ct pointer to output cipher text to used for decapsulation [out] ss pointer to output shared secret that will be also produced during decapsulation [in] ss_len length of shared secret to be generated [in] pk pointer to input public key
Returns 0 (success) or < 0 on error
◆ lc_kyber_512_ies_dec()
| int lc_kyber_512_ies_dec | ( | const struct lc_kyber_512_sk * | sk, |
| const struct lc_kyber_512_ct * | ct, | ||
| const uint8_t * | ciphertext, | ||
| uint8_t * | plaintext, | ||
| size_t | datalen, | ||
| const uint8_t * | aad, | ||
| size_t | aadlen, | ||
| const uint8_t * | tag, | ||
| size_t | taglen, | ||
| struct lc_aead_ctx * | aead ) |
lc_kyber_ies_dec - KyberIES decryption oneshot
The implementation supports an in-place data decryption where the plaintext and ciphertext buffer pointers refer to the same memory location.
The function entirely operates on stack memory.
- Parameters
-
[in] sk Kyber secret key of data owner [in] ct Kyber ciphertext received from the encryption operation [in] ciphertext Ciphertext data to be encrypted [out] plaintext Buffer of equal size as ciphertext that will be filled with the decryption result [in] datalen Length of the ciphertext buffer [in] aad Additional authenticate data to be processed - this is data which is not encrypted, but considered as part of the authentication. [in] aadlen Length of the AAD buffer [in] tag Buffer with the authentication tag [in] taglen Length of the tag buffer [in] aead Allocated AEAD algorithm - the caller only needs to provide an allocated but otherwise unused instance of an AEAD algorithm. This allows the caller to define the AEAD algorithm type. The caller must zeroize and release the context after completion.
- Returns
- 0 on success, < 0 on error (-EBADMSG on integrity error)
◆ lc_kyber_512_ies_dec_final()
|
inlinestatic |
lc_kyber_ies_dec_final - KyberIES decryption stream operation finalization / integrity test
The implementation supports an in-place data decryption where the plaintext and ciphertext buffer pointers refer to the same memory location.
The function entirely operates on stack memory.
- Parameters
-
[in] aead Allocated AEAD algorithm - the caller only needs to provide an allocated but otherwise unused instance of an AEAD algorithm. This allows the caller to define the AEAD algorithm type. The caller must zeroize and release the context after completion. [in] tag Buffer with the authentication tag [in] taglen Length of the tag buffer
- Returns
- 0 on success, < 0 on error (-EBADMSG on integrity error)
Definition at line 760 of file lc_kyber_512.h.
◆ lc_kyber_512_ies_dec_init()
| int lc_kyber_512_ies_dec_init | ( | struct lc_aead_ctx * | aead, |
| const struct lc_kyber_512_sk * | sk, | ||
| const struct lc_kyber_512_ct * | ct, | ||
| const uint8_t * | aad, | ||
| size_t | aadlen ) |
lc_kyber_ies_dec_init - KyberIES decryption stream operation initialization
The implementation supports an in-place data decryption where the plaintext and ciphertext buffer pointers refer to the same memory location.
The function entirely operates on stack memory.
The aead context is initialized such that it can be used with lc_kyber_512_ies_dec_[update|final].
- Parameters
-
[out] aead Allocated AEAD algorithm - the caller only needs to provide an allocated but otherwise unused instance of an AEAD algorithm. This allows the caller to define the AEAD algorithm type. The caller must zeroize and release the context after completion. [in] sk Kyber secret key of data owner [in] ct Kyber ciphertext received from the encryption operation [in] aad Additional authenticate data to be processed - this is data which is not encrypted, but considered as part of the authentication. [in] aadlen Length of the AAD buffer
- Returns
- 0 on success, < 0 on error
◆ lc_kyber_512_ies_dec_update()
|
inlinestatic |
lc_kyber_ies_dec_update - KyberIES decryption stream operation add more data
The implementation supports an in-place data decryption where the plaintext and ciphertext buffer pointers refer to the same memory location.
The function entirely operates on stack memory.
- Parameters
-
[in] aead Allocated AEAD algorithm - the caller only needs to provide an allocated but otherwise unused instance of an AEAD algorithm. This allows the caller to define the AEAD algorithm type. The caller must zeroize and release the context after completion. [in] ciphertext Ciphertext data to be encrypted [out] plaintext Buffer of equal size as ciphertext that will be filled with the decryption result [in] datalen Length of the ciphertext buffer
- Returns
- 0 on success, < 0 on error
Definition at line 734 of file lc_kyber_512.h.
◆ lc_kyber_512_ies_enc()
| int lc_kyber_512_ies_enc | ( | const struct lc_kyber_512_pk * | pk, |
| struct lc_kyber_512_ct * | ct, | ||
| const uint8_t * | plaintext, | ||
| uint8_t * | ciphertext, | ||
| size_t | datalen, | ||
| const uint8_t * | aad, | ||
| size_t | aadlen, | ||
| uint8_t * | tag, | ||
| size_t | taglen, | ||
| struct lc_aead_ctx * | aead ) |
lc_kyber_ies_enc - KyberIES encryption oneshot
The implementation supports an in-place data encryption where the plaintext and ciphertext buffer pointers refer to the same memory location.
The function entirely operates on stack memory.
- Parameters
-
[in] pk Kyber public key of data owner [out] ct Kyber ciphertext to be sent to the decryption operation [in] plaintext Plaintext data to be encrypted [out] ciphertext Buffer of equal size as plaintext that will be filled with the encryption result [in] datalen Length of the plaintext buffer [in] aad Additional authenticate data to be processed - this is data which is not encrypted, but considered as part of the authentication. [in] aadlen Length of the AAD buffer [out] tag Buffer that will be filled with the authentication tag [in] taglen Length of the tag buffer [in] aead Allocated AEAD algorithm - the caller only needs to provide an allocated but otherwise unused instance of an AEAD algorithm. This allows the caller to define the AEAD algorithm type. The caller must zeroize and release the context after completion.
- Returns
- 0 on success, < 0 on error
◆ lc_kyber_512_ies_enc_final()
|
inlinestatic |
lc_kyber_ies_enc_final - KyberIES encryption stream operation finalization / integrity test
The implementation supports an in-place data encryption where the plaintext and ciphertext buffer pointers refer to the same memory location.
The function entirely operates on stack memory.
- Parameters
-
[in] aead Allocated AEAD algorithm - the caller only needs to provide an allocated but otherwise unused instance of an AEAD algorithm. This allows the caller to define the AEAD algorithm type. The caller must zeroize and release the context after completion. [out] tag Buffer that will be filled with the authentication tag [in] taglen Length of the tag buffer
- Returns
- 0 on success, < 0 on error
Definition at line 644 of file lc_kyber_512.h.
◆ lc_kyber_512_ies_enc_init()
| int lc_kyber_512_ies_enc_init | ( | struct lc_aead_ctx * | aead, |
| const struct lc_kyber_512_pk * | pk, | ||
| struct lc_kyber_512_ct * | ct, | ||
| const uint8_t * | aad, | ||
| size_t | aadlen ) |
lc_kyber_ies_enc_init - KyberIES encryption stream operation initialization
The implementation supports an in-place data encryption where the plaintext and ciphertext buffer pointers refer to the same memory location.
The function entirely operates on stack memory.
The aead context is initialized such that it can be used with lc_kyber_ies_enc_[update|final].
- Parameters
-
[out] aead Allocated AEAD algorithm - the caller only needs to provide an allocated but otherwise unused instance of an AEAD algorithm. This allows the caller to define the AEAD algorithm type. The caller must zeroize and release the context after completion. [in] pk Kyber public key of data owner [out] ct Kyber ciphertext to be sent to the decryption operation [in] aad Additional authenticate data to be processed - this is data which is not encrypted, but considered as part of the authentication. [in] aadlen Length of the AAD buffer
- Returns
- 0 on success, < 0 on error
◆ lc_kyber_512_ies_enc_update()
|
inlinestatic |
lc_kyber_ies_enc_update - KyberIES encryption stream operation add more data
The implementation supports an in-place data encryption where the plaintext and ciphertext buffer pointers refer to the same memory location.
The function entirely operates on stack memory.
- Parameters
-
[in] aead Allocated AEAD algorithm - the caller only needs to provide an allocated but otherwise unused instance of an AEAD algorithm. This allows the caller to define the AEAD algorithm type. The caller must zeroize and release the context after completion. [in] plaintext Plaintext data to be encrypted [out] ciphertext Buffer of equal size as plaintext that will be filled with the encryption result [in] datalen Length of the plaintext buffer
- Returns
- 0 on success, < 0 on error
Definition at line 618 of file lc_kyber_512.h.
◆ lc_kyber_512_keypair()
| int lc_kyber_512_keypair | ( | struct lc_kyber_512_pk * | pk, |
| struct lc_kyber_512_sk * | sk, | ||
| struct lc_rng_ctx * | rng_ctx ) |
lc_kyber_keypair - Generates public and private key for IND-CCA2-secure Kyber key encapsulation mechanism
- Parameters
-
[out] pk pointer to already allocated output public key [out] sk pointer to already allocated output private key [in] rng_ctx pointer to seeded random number generator context
- Returns
- 0 (success) or < 0 on error
◆ lc_kyber_512_keypair_from_seed()
| int lc_kyber_512_keypair_from_seed | ( | struct lc_kyber_512_pk * | pk, |
| struct lc_kyber_512_sk * | sk, | ||
| const uint8_t * | seed, | ||
| size_t | seedlen ) |
lc_kyber__keypair_from_seed - Generates Kyber public and private key from a given seed.
The idea of the function is the allowance of FIPS 203 to maintain the seed used to generate a key pair in lieu of maintaining a private key or the key pair (which used much more memory). The seed must be treated equally sensitive as a private key.
The seed is generated by simply obtaining 64 bytes from a properly seeded DRNG, i.e. the same way as a symmetric key would be generated.
- Parameters
-
[out] pk pointer to allocated output public key [out] sk pointer to allocated output private key [in] seed buffer with the seed data which must be exactly 64 bytes in size [in] seedlen length of the seed buffer
- Returns
- 0 (success) or < 0 on error
◆ lc_kyber_512_pk_size()
|
inlinestatic |
Return the size of the Kyber public key.
Definition at line 154 of file lc_kyber_512.h.
◆ lc_kyber_512_sk_size()
|
inlinestatic |
Return the size of the Kyber secret key.
Definition at line 145 of file lc_kyber_512.h.
◆ lc_kyber_512_ss_size()
|
inlinestatic |
Return the size of the Kyber shared secret.
Definition at line 172 of file lc_kyber_512.h.
◆ lc_kyber_512_x25519_dec_kdf()
| int lc_kyber_512_x25519_dec_kdf | ( | uint8_t * | ss, |
| size_t | ss_len, | ||
| const struct lc_kyber_512_x25519_ct * | ct, | ||
| const struct lc_kyber_512_x25519_sk * | sk ) |
lc_kyber_x25519_dec_kdf - Key decapsulation with KDF applied to shared secret
Generates cipher text and shared secret for given private key. The shared secret is derived from the Kyber SS using the KDF derived from the round 3 definition of Kyber:
SS <- KMAC256(K = Kyber-SS || X25519-SS, X = Kyber-CT,
L = requested SS length, S = "Kyber KEM Double SS")
- Parameters
-
[out] ss pointer to output shared secret that is the same as produced during encapsulation [in] ss_len length of shared secret to be generated [in] ct pointer to input cipher text generated during encapsulation [in] sk pointer to input private key
- Returns
- 0
On failure, ss will contain a pseudo-random value.
◆ lc_kyber_512_x25519_enc_kdf()
| int lc_kyber_512_x25519_enc_kdf | ( | struct lc_kyber_512_x25519_ct * | ct, |
| uint8_t * | ss, | ||
| size_t | ss_len, | ||
| const struct lc_kyber_512_x25519_pk * | pk ) |
lc_kyber_x25519_enc_kdf - Key encapsulation with KDF applied to shared secret
Generates cipher text and shared secret for given public key. The shared secret is derived from the Kyber SS using the KDF derived from the round 3 definition of Kyber:
SS <- KMAC256(K = Kyber-SS || X25519-SS, X = Kyber-CT,
L = requested SS length, S = "Kyber KEM Double SS")
NOTE: The concatenatino of Kyber-SS || ECC-SS complies with SP800-56C rev 2 chapter 2 defining the hybrid shared secret of the form Z' = Z || T where Z is the "standard shared secret" from Kyber followed by the auxiliary shared secret T that has been generated by some other method.
- Parameters
-
[out] ct pointer to output cipher text to used for decapsulation [out] ss pointer to output shared secret that will be also produced during decapsulation [in] ss_len length of shared secret to be generated [in] pk pointer to input public key
Returns 0 (success) or < 0 on error
◆ lc_kyber_512_x25519_ies_dec()
| int lc_kyber_512_x25519_ies_dec | ( | const struct lc_kyber_512_x25519_sk * | sk, |
| const struct lc_kyber_512_x25519_ct * | ct, | ||
| const uint8_t * | ciphertext, | ||
| uint8_t * | plaintext, | ||
| size_t | datalen, | ||
| const uint8_t * | aad, | ||
| size_t | aadlen, | ||
| const uint8_t * | tag, | ||
| size_t | taglen, | ||
| struct lc_aead_ctx * | aead ) |
lc_kyber_x25519_ies_dec - KyberIES decryption oneshot
The implementation supports an in-place data decryption where the plaintext and ciphertext buffer pointers refer to the same memory location.
The function entirely operates on stack memory.
- Parameters
-
[in] sk Kyber secret key of data owner [in] ct Kyber ciphertext received from the encryption operation [in] ciphertext Ciphertext data to be encrypted [out] plaintext Buffer of equal size as ciphertext that will be filled with the decryption result [in] datalen Length of the ciphertext buffer [in] aad Additional authenticate data to be processed - this is data which is not encrypted, but considered as part of the authentication. [in] aadlen Length of the AAD buffer [in] tag Buffer with the authentication tag [in] taglen Length of the tag buffer [in] aead Allocated AEAD algorithm - the caller only needs to provide an allocated but otherwise unused instance of an AEAD algorithm. This allows the caller to define the AEAD algorithm type. The caller must zeroize and release the context after completion.
- Returns
- 0 on success, < 0 on error (-EBADMSG on integrity error)
◆ lc_kyber_512_x25519_ies_dec_final()
|
inlinestatic |
lc_kyber _x25519_ies_dec_final - KyberIES decryption stream operation finalization / integrity test
The implementation supports an in-place data decryption where the plaintext and ciphertext buffer pointers refer to the same memory location.
The function entirely operates on stack memory.
- Parameters
-
[in] aead Allocated AEAD algorithm - the caller only needs to provide an allocated but otherwise unused instance of an AEAD algorithm. This allows the caller to define the AEAD algorithm type. The caller must zeroize and release the context after completion. [in] tag Buffer with the authentication tag [in] taglen Length of the tag buffer
- Returns
- 0 on success, < 0 on error (-EBADMSG on integrity error)
Definition at line 1268 of file lc_kyber_512.h.
◆ lc_kyber_512_x25519_ies_dec_init()
| int lc_kyber_512_x25519_ies_dec_init | ( | struct lc_aead_ctx * | aead, |
| const struct lc_kyber_512_x25519_sk * | sk, | ||
| const struct lc_kyber_512_x25519_ct * | ct, | ||
| const uint8_t * | aad, | ||
| size_t | aadlen ) |
lc_kyber_x25519_ies_dec_init - KyberIES decryption stream operation initialization
The implementation supports an in-place data decryption where the plaintext and ciphertext buffer pointers refer to the same memory location.
The function entirely operates on stack memory.
The aead context is initialized such that it can be used with lc_kyber_x25519_ies_dec_[update|final].
- Parameters
-
[out] aead Allocated AEAD algorithm - the caller only needs to provide an allocated but otherwise unused instance of an AEAD algorithm. This allows the caller to define the AEAD algorithm type. The caller must zeroize and release the context after completion. [in] sk Kyber secret key of data owner [in] ct Kyber ciphertext received from the encryption operation [in] aad Additional authenticate data to be processed - this is data which is not encrypted, but considered as part of the authentication. [in] aadlen Length of the AAD buffer
- Returns
- 0 on success, < 0 on error
◆ lc_kyber_512_x25519_ies_dec_update()
|
inlinestatic |
lc_kyber_x25519_ies_dec_update - KyberIES decryption stream operation add more data
The implementation supports an in-place data decryption where the plaintext and ciphertext buffer pointers refer to the same memory location.
The function entirely operates on stack memory.
- Parameters
-
[in] aead Allocated AEAD algorithm - the caller only needs to provide an allocated but otherwise unused instance of an AEAD algorithm. This allows the caller to define the AEAD algorithm type. The caller must zeroize and release the context after completion. [in] ciphertext Ciphertext data to be encrypted [out] plaintext Buffer of equal size as ciphertext that will be filled with the decryption result [in] datalen Length of the ciphertext buffer
- Returns
- 0 on success, < 0 on error
Definition at line 1241 of file lc_kyber_512.h.
◆ lc_kyber_512_x25519_ies_enc()
| int lc_kyber_512_x25519_ies_enc | ( | const struct lc_kyber_512_x25519_pk * | pk, |
| struct lc_kyber_512_x25519_ct * | ct, | ||
| const uint8_t * | plaintext, | ||
| uint8_t * | ciphertext, | ||
| size_t | datalen, | ||
| const uint8_t * | aad, | ||
| size_t | aadlen, | ||
| uint8_t * | tag, | ||
| size_t | taglen, | ||
| struct lc_aead_ctx * | aead ) |
lc_kyber_x25519_ies_enc - KyberIES encryption oneshot
The implementation supports an in-place data encryption where the plaintext and ciphertext buffer pointers refer to the same memory location.
The function entirely operates on stack memory.
- Parameters
-
[in] pk Kyber public key of data owner [out] ct Kyber ciphertext to be sent to the decryption operation [in] plaintext Plaintext data to be encrypted [out] ciphertext Buffer of equal size as plaintext that will be filled with the encryption result [in] datalen Length of the plaintext buffer [in] aad Additional authenticate data to be processed - this is data which is not encrypted, but considered as part of the authentication. [in] aadlen Length of the AAD buffer [out] tag Buffer that will be filled with the authentication tag [in] taglen Length of the tag buffer [in] aead Allocated AEAD algorithm - the caller only needs to provide an allocated but otherwise unused instance of an AEAD algorithm. This allows the caller to define the AEAD algorithm type. The caller must zeroize and release the context after completion.
- Returns
- 0 on success, < 0 on error
◆ lc_kyber_512_x25519_ies_enc_final()
|
inlinestatic |
lc_kyber_x25519_ies_enc_final - KyberIES encryption stream operation finalization / integrity test
The implementation supports an in-place data encryption where the plaintext and ciphertext buffer pointers refer to the same memory location.
The function entirely operates on stack memory.
- Parameters
-
[in] aead Allocated AEAD algorithm - the caller only needs to provide an allocated but otherwise unused instance of an AEAD algorithm. This allows the caller to define the AEAD algorithm type. The caller must zeroize and release the context after completion. [out] tag Buffer that will be filled with the authentication tag [in] taglen Length of the tag buffer
- Returns
- 0 on success, < 0 on error
Definition at line 1148 of file lc_kyber_512.h.
◆ lc_kyber_512_x25519_ies_enc_init()
| int lc_kyber_512_x25519_ies_enc_init | ( | struct lc_aead_ctx * | aead, |
| const struct lc_kyber_512_x25519_pk * | pk, | ||
| struct lc_kyber_512_x25519_ct * | ct, | ||
| const uint8_t * | aad, | ||
| size_t | aadlen ) |
lc_kyber_x25519_ies_enc_init - KyberIES encryption stream operation initialization
The implementation supports an in-place data encryption where the plaintext and ciphertext buffer pointers refer to the same memory location.
The function entirely operates on stack memory.
The aead context is initialized such that it can be used with lc_kyber_x25519_ies_enc_[update|final].
- Parameters
-
[out] aead Allocated AEAD algorithm - the caller only needs to provide an allocated but otherwise unused instance of an AEAD algorithm. This allows the caller to define the AEAD algorithm type. The caller must zeroize and release the context after completion. [in] pk Kyber public key of data owner [out] ct Kyber ciphertext to be sent to the decryption operation [in] aad Additional authenticate data to be processed - this is data which is not encrypted, but considered as part of the authentication. [in] aadlen Length of the AAD buffer
- Returns
- 0 on success, < 0 on error
◆ lc_kyber_512_x25519_ies_enc_update()
|
inlinestatic |
lc_kyber_x25519_ies_enc_update - KyberIES encryption stream operation add more data
The implementation supports an in-place data encryption where the plaintext and ciphertext buffer pointers refer to the same memory location.
The function entirely operates on stack memory.
- Parameters
-
[in] aead Allocated AEAD algorithm - the caller only needs to provide an allocated but otherwise unused instance of an AEAD algorithm. This allows the caller to define the AEAD algorithm type. The caller must zeroize and release the context after completion. [in] plaintext Plaintext data to be encrypted [out] ciphertext Buffer of equal size as plaintext that will be filled with the encryption result [in] datalen Length of the plaintext buffer
Definition at line 1121 of file lc_kyber_512.h.
◆ lc_kyber_512_x25519_keypair()
| int lc_kyber_512_x25519_keypair | ( | struct lc_kyber_512_x25519_pk * | pk, |
| struct lc_kyber_512_x25519_sk * | sk, | ||
| struct lc_rng_ctx * | rng_ctx ) |
lc_kyber_x25519_keypair - Generates public and private key for IND-CCA2-secure Kyber key encapsulation mechanism
- Parameters
-
[out] pk pointer to already allocated output public key [out] sk pointer to already allocated output private key [in] rng_ctx pointer to seeded random number generator context
- Returns
- 0 (success) or < 0 on error
Generated by