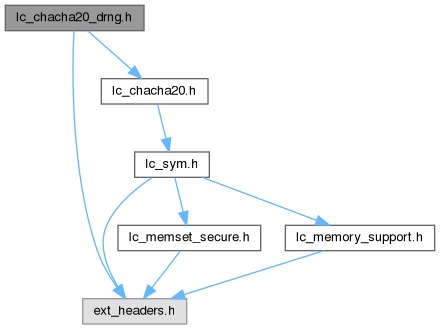
Include dependency graph for lc_chacha20_drng.h:
Include dependency graph for lc_chacha20_drng.h:Go to the source code of this file.
Macros | |
| #define | LC_CC20_DRNG_CTX_ON_STACK(name) |
| Allocate stack memory for the ChaCha20 context. | |
Functions | |
| static void | lc_cc20_drng_zero (struct lc_chacha20_drng_ctx *cc20_ctx) |
| Zeroize ChaCha20 DRNG context allocated with either LC_CC20_DRNG_CTX_ON_STACK or lc_cc20_drng_alloc. | |
| int | lc_cc20_drng_alloc (struct lc_chacha20_drng_ctx **cc20_ctx) |
| Allocation of a ChaCha20 DRNG context. | |
| void | lc_cc20_drng_zero_free (struct lc_chacha20_drng_ctx *cc20_ctx) |
| Zeroize and free ChaCha20 DRNG context. | |
| void | lc_cc20_drng_generate (struct lc_chacha20_drng_ctx *cc20_ctx, uint8_t *outbuf, size_t outbuflen) |
| Obtain random numbers. | |
| void | lc_cc20_drng_seed (struct lc_chacha20_drng_ctx *cc20_ctx, const uint8_t *inbuf, size_t inbuflen) |
| Reseed the ChaCha20 DRNG. | |
Macro Definition Documentation
◆ LC_CC20_DRNG_CTX_ON_STACK
| #define LC_CC20_DRNG_CTX_ON_STACK | ( | name | ) |
Allocate stack memory for the ChaCha20 context.
- Parameters
-
[in] name Name of the stack variable
- Warning
- You MUST seed the DRNG!
Definition at line 69 of file lc_chacha20_drng.h.
Function Documentation
◆ lc_cc20_drng_alloc()
| int lc_cc20_drng_alloc | ( | struct lc_chacha20_drng_ctx ** | cc20_ctx | ) |
Allocation of a ChaCha20 DRNG context.
- Parameters
-
[out] cc20_ctx ChaCha20 DRNG context allocated by the function
The cipher handle including its memory is allocated with this function.
The memory is pinned so that the DRNG state cannot be swapped out to disk.
- Warning
- You MUST seed the DRNG!
- Returns
- 0 upon success; < 0 on error
◆ lc_cc20_drng_generate()
| void lc_cc20_drng_generate | ( | struct lc_chacha20_drng_ctx * | cc20_ctx, |
| uint8_t * | outbuf, | ||
| size_t | outbuflen ) |
Obtain random numbers.
- Parameters
-
[in] cc20_ctx allocated ChaCha20 cipher handle [out] outbuf allocated buffer that is to be filled with random numbers [in] outbuflen length of outbuf indicating the size of the random number byte string to be generated
Generate random numbers and fill the buffer provided by the caller.
After the generation of random numbers, the internal state of the ChaCha20 DRNG is completely re-created using ChaCha20 to provide enhanced backtracking resistance. I.e. if the state of the DRNG becomes known after generation of random numbers, an attacker cannot deduce the already generated random numbers.
◆ lc_cc20_drng_seed()
| void lc_cc20_drng_seed | ( | struct lc_chacha20_drng_ctx * | cc20_ctx, |
| const uint8_t * | inbuf, | ||
| size_t | inbuflen ) |
Reseed the ChaCha20 DRNG.
- Parameters
-
[in] cc20_ctx allocated ChaCha20 cipher handle [in] inbuf buffer with the seed data [in] inbuflen length of inbuf
When calling the function, the DRNG is seeded or reseeded. If it is reseeded, the old state information is mixed into the new state.
◆ lc_cc20_drng_zero()
|
inlinestatic |
Zeroize ChaCha20 DRNG context allocated with either LC_CC20_DRNG_CTX_ON_STACK or lc_cc20_drng_alloc.
- Parameters
-
[in] cc20_ctx Hash context to be zeroized
Definition at line 52 of file lc_chacha20_drng.h.
◆ lc_cc20_drng_zero_free()
| void lc_cc20_drng_zero_free | ( | struct lc_chacha20_drng_ctx * | cc20_ctx | ) |
Zeroize and free ChaCha20 DRNG context.
- Parameters
-
[in] cc20_ctx ChaCha20 DRNG context to be zeroized and freed
Generated by